Introduction
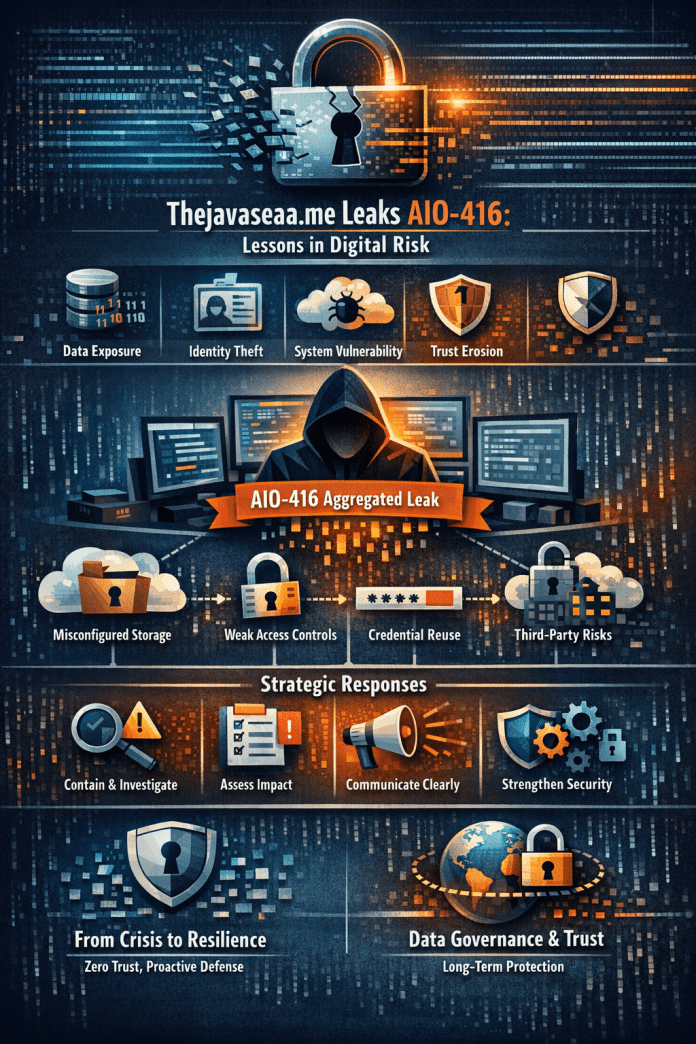
The rise of large-scale data exposure events has fundamentally reshaped how organizations and individuals think about cybersecurity. One topic increasingly drawing attention in digital security discussions is thejavasea.me leaks aio-416. While surface-level conversations often focus on shock value or speculation, the real importance lies in understanding the structural, operational, and strategic implications of such incidents.
Digital leaks are rarely isolated events. They are signals indicators of systemic vulnerabilities, governance failures, or inadequate digital risk frameworks. When references to thejavasea.me leaks aio-416 appear in online communities, the underlying concern is not just about leaked data, but about infrastructure weaknesses and trust erosion.
This article provides a comprehensive, expert-level examination of the topic. We will break down what it represents, why it matters, who it impacts, and how organizations should strategically respond. Rather than speculation, this guide focuses on risk analysis, security frameworks, and long-term resilience.
Understanding Thejavasea.me Leaks AIO-416
At its core, the phrase thejavasea.me leaks aio-416 appears to refer to a reported data exposure associated with a specific digital environment or repository. The designation “AIO-416” suggests a categorized or compiled dataset potentially an “All-In-One” archive tied to a specific identifier.
In cybersecurity terminology, leaks often involve:
- Unauthorized access to stored data
- Public exposure of previously private information
- Compiled datasets redistributed through third-party channels
- Aggregated credential or content collections
The critical distinction is between a breach and a leak. A breach typically implies unauthorized system intrusion. A leak may result from external compromise, insider action, misconfiguration, or intentional publication.
Understanding this distinction is essential because response strategies differ significantly depending on the origin and architecture of exposure.
The Structural Nature of Digital Leak Events
When examining references to thejavasea.me leaks aio-416, the strategic question becomes: What systemic weaknesses allow such events to occur?
Modern digital ecosystems are interconnected. A vulnerability in one layer can expose entire networks. Common structural weaknesses include:
1. Misconfigured Cloud Storage
Publicly accessible storage buckets remain one of the most common causes of mass data exposure.
2. Inadequate Access Controls
Over-permissioned user accounts dramatically increase insider threat risk.
3. Credential Reuse
Reused passwords across platforms amplify impact when one system is compromised.
4. Weak Data Segmentation
Lack of compartmentalization enables attackers to move laterally within systems.
The reference to a labeled dataset such as AIO-416 suggests possible aggregation meaning exposure may involve compiled information rather than isolated files. Aggregated leaks carry higher risk due to contextualization of data.
Who Is Impacted by Events Like Thejavasea.me Leaks AIO-416?
Digital leak events rarely affect a single stakeholder group. Impact typically spans multiple layers:
Individuals
If personal data is included, consequences may involve identity theft, phishing, reputational harm, or financial fraud.
Organizations
Brand trust, regulatory scrutiny, and financial liability become immediate concerns.
Third-Party Partners
Supply chain security risks emerge when interconnected vendors share compromised data channels.
Digital Platforms
Search engines and hosting providers face pressure to manage indexing and distribution responsibly.
The broader issue is trust fragmentation. Once users believe data environments are unsafe, long-term brand damage becomes more costly than immediate financial loss.
Strategic Risk Dimensions
A mature analysis of thejavasea.me leaks aio-416 requires evaluating multiple risk categories.
Operational Risk
Disrupted services, forced system audits, emergency security upgrades.
Legal and Compliance Risk
Data protection regulations increasingly impose strict penalties for negligence.
Reputational Risk
Loss of consumer confidence can outlast technical remediation.
Financial Risk
Incident response costs, litigation exposure, and long-term customer churn.
Many organizations underestimate reputational recovery timelines. Technical repair can take weeks. Trust rebuilding may take years.
Common Misconceptions About Digital Leaks
Public discussions around incidents like thejavasea.me leaks aio-416 often include misleading assumptions.
Misconception 1: Only Large Companies Are Targets
In reality, small and mid-sized entities are often more vulnerable due to limited security budgets.
Misconception 2: Encryption Alone Prevents Leaks
Encryption protects data in transit and at rest but misconfigured access policies can still expose decrypted information.
Misconception 3: Once Removed, Risk Disappears
Data replication across multiple platforms means leaked content may persist indefinitely.
Misconception 4: It’s Always a Sophisticated Hack
Human error remains one of the most common causes of exposure.
Understanding these misconceptions helps organizations avoid reactive thinking and focus on systemic prevention.
Methodology for Responding to Large-Scale Leak Events
When an incident like thejavasea.me leaks aio-416 surfaces, a structured response is critical. Effective crisis management follows a disciplined sequence:
Step 1: Immediate Containment
Disable compromised access points and isolate affected systems.
Step 2: Forensic Investigation
Identify entry vectors, scope of exposure, and duration of vulnerability.
Step 3: Impact Assessment
Determine which data categories were affected and who is at risk.
Step 4: Stakeholder Communication
Transparent, accurate communication reduces speculation and reputational damage.
Step 5: Long-Term Hardening
Implement architecture redesign, not just temporary fixes.
Organizations that skip forensic depth often experience repeat incidents within 12–24 months.
Preventative Architecture: Designing for Resilience
Preventing recurrence requires more than patching vulnerabilities. It requires structural redesign.
Zero-Trust Security Model
No user or device is trusted by default even inside the network perimeter.
Role-Based Access Control (RBAC)
Access granted strictly based on job necessity.
Continuous Monitoring
Real-time behavioral anomaly detection.
Data Minimization
Store only what is essential. The less data retained, the lower the exposure risk.
Regular Security Audits
Independent assessments reduce blind spots.
Resilience is not achieved through single tools. It emerges from layered defense architecture.
Organizational Transformation After a Leak
Serious incidents often become catalysts for digital transformation. The most resilient organizations use events like thejavasea.me leaks aio-416 as turning points rather than crises.
Post-incident transformation typically includes:
- Executive-level cybersecurity oversight
- Budget reallocation toward proactive risk management
- Formalized incident response playbooks
- Cultural shifts emphasizing data stewardship
Cybersecurity maturity is not defined by absence of incidents, but by speed and intelligence of response.
Authority and Trust: Why This Topic Matters in the Modern Digital Economy
Digital trust has become a competitive differentiator. Consumers increasingly choose services based on perceived data safety.
Events like thejavasea.me leaks aio-416 highlight several modern realities:
First, data is a high-value asset and therefore a high-value target.
Second, regulatory environments worldwide are tightening.
Third, AI-driven data analysis increases both value and risk of exposed datasets.
From a governance perspective, leak events should be evaluated not just as technical failures but as enterprise risk management failures.
Ethical responsibility also plays a role. Organizations that collect data assume a custodial duty. Transparency, accountability, and long-term safeguards are no longer optional they are expected.
Companies that embed privacy-by-design and security-by-design principles outperform reactive competitors in long-term resilience metrics.
Frequently Asked Questions
1. What is thejavasea.me leaks aio-416?
Thejavasea.me leaks aio-416 appears to reference a categorized data exposure event involving a compiled dataset. The “AIO” designation suggests aggregated information, which may increase risk due to data consolidation. Understanding its structure helps assess potential security and privacy implications.
2. Is thejavasea.me leaks aio-416 considered a data breach?
Not necessarily. A breach involves unauthorized intrusion, while a leak may result from misconfiguration, insider action, or redistribution of data. Determining whether thejavasea.me leaks aio-416 qualifies as a breach depends on forensic investigation findings.
3. Who is most at risk from thejavasea.me leaks aio-416?
Risk depends on the data involved. Individuals may face identity fraud or phishing attempts, while organizations could encounter reputational and compliance risks. Aggregated datasets increase exposure impact because they provide structured, usable information.
4. How should organizations respond to incidents like thejavasea.me leaks aio-416?
Organizations should initiate containment, conduct forensic audits, assess impact, communicate transparently, and strengthen long-term architecture. A structured response reduces repeat vulnerabilities and restores stakeholder confidence more effectively than reactive patching.
5. Can leaked data from thejavasea.me leaks aio-416 be fully removed from the internet?
Complete removal is extremely difficult once data is replicated. Even if primary sources delete content, redistributed copies may persist across platforms. Risk mitigation typically focuses on damage control rather than total eradication.
6. What long-term lessons does thejavasea.me leaks aio-416 highlight?
It underscores the importance of zero-trust architecture, strict access controls, data minimization, and continuous monitoring. Sustainable cybersecurity maturity requires proactive governance rather than reactive crisis management.
Conclusion
The discussion surrounding thejavasea.me leaks aio-416 reflects a broader shift in how digital risk is perceived and managed. Data exposure events are no longer isolated technical failures they are enterprise-level governance challenges.
Organizations that treat leak incidents as strategic inflection points build stronger infrastructure, deeper stakeholder trust, and long-term resilience. Those that rely on short-term containment risk recurrence and escalating damage.
In a world where data is both asset and liability, cybersecurity is not merely an IT function it is a core leadership responsibility. Understanding the implications of events like thejavasea.me leaks aio-416 is the first step toward building systems designed not just to function, but to endure