Introduction
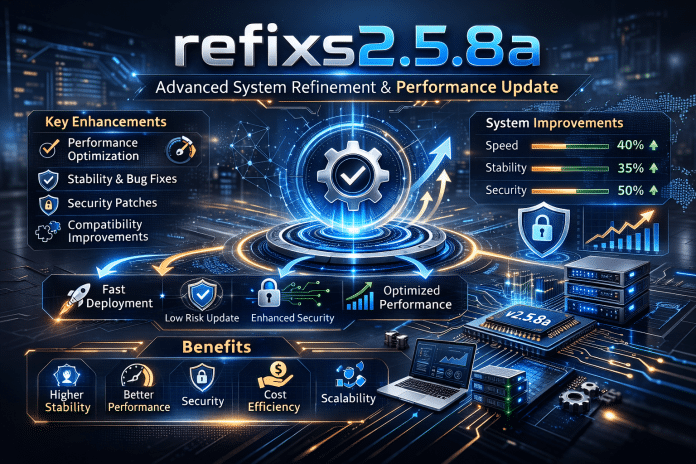
Software version identifiers often appear simple on the surface, yet behind each structured release lies a series of technical refinements, architectural decisions, and strategic objectives. When professionals search for refixs2.5.8a, they are typically seeking clarity: what it represents, how it differs from prior iterations, and why it matters in operational or development environments.
Understanding refixs2.5.8a requires more than reading a changelog. It involves analyzing release intent, structural adjustments, compatibility implications, and long-term system impact. Whether deployed in enterprise systems, development frameworks, or performance-driven environments, version-level updates can influence stability, security posture, and scalability.
This article provides a comprehensive, expert-level breakdown of refixs2.5.8a covering its conceptual foundation, implementation logic, measurable benefits, risk considerations, and long-term organizational implications. The goal is not simply to describe the version but to explain its strategic value in practical terms.
Understanding refixs2.5.8a: What It Represents
At its core, refixs2.5.8a represents a structured version release that signals targeted refinement rather than full-scale architectural overhaul.
Version structures typically follow semantic principles:
- Major version (2) – Indicates foundational stability and maturity.
- Minor version (5) – Suggests iterative enhancement or capability expansion.
- Patch level (8) – Signals performance tuning, bug resolution, or minor improvements.
- Suffix (a) – Often denotes a hotfix, corrective patch, or rapid-response stabilization update.
This layered structure communicates precision. Instead of introducing disruptive change, refixs2.5.8a likely focuses on optimizing existing systems while minimizing operational risk.
In professional environments, this distinction matters. Organizations rely on predictable upgrade cycles. Minor patches must deliver improvement without introducing systemic instability.
Core Objectives Behind refixs2.5.8a
Refined version updates typically pursue one or more of the following strategic objectives:
1. Performance Optimization
Micro-adjustments to processing logic, memory allocation, or resource handling can yield measurable gains in throughput and response times.
2. Stability Enhancement
Patch-level releases often address edge-case failures discovered in real-world deployment. These are rarely theoretical; they are identified through operational feedback loops.
3. Security Hardening
Modern environments require continuous vulnerability mitigation. Even minor updates may include silent but critical security reinforcements.
4. Compatibility Refinement
As ecosystems evolve, dependencies shift. refixs2.5.8a may include improved interoperability with updated libraries, frameworks, or infrastructure layers.
The strategic nature of such updates lies in incremental improvement without architectural disruption.
Methodology Behind a Release Like refixs2.5.8a
Professionally managed releases typically follow a disciplined lifecycle:
Development and Internal Testing
Engineering teams identify performance anomalies or reported issues. Fixes are developed in controlled branches and tested through:
- Unit testing
- Regression testing
- Performance benchmarking
- Security validation
Controlled Rollout
Before general release, controlled environments or staging deployments validate stability under production-like conditions.
Monitoring and Feedback
After deployment, telemetry and usage analytics determine whether the improvements achieve measurable results.
This structured methodology ensures that refixs2.5.8a is not simply a reactive patch but a validated refinement.
Who refixs2.5.8a Is Designed For
Version-level updates serve multiple stakeholders:
Development Teams
Developers benefit from improved reliability, reduced debugging overhead, and smoother integration.
System Administrators
Operational teams value predictable upgrades that reduce system downtime or performance volatility.
Enterprise Decision-Makers
Leadership prioritizes risk mitigation, compliance alignment, and long-term stability over feature novelty.
High-Availability Environments
Organizations operating mission-critical systems depend on incremental updates that strengthen resilience without forcing architectural rewrites.
Understanding the intended audience clarifies the importance of refixs2.5.8a within broader technology strategy.
Measurable Benefits and Operational Outcomes
While minor releases rarely introduce visible features, their impact can be significant.
Reduced Error Rates
Correcting edge-case logic can lower incident frequency across distributed environments.
Improved System Efficiency
Performance refinements often reduce resource consumption, translating into infrastructure cost savings over time.
Lower Maintenance Overhead
Stable systems require fewer emergency interventions. This frees technical teams to focus on innovation instead of reactive troubleshooting.
Enhanced Security Posture
Subtle security fixes strengthen defense-in-depth strategies and reduce exposure to exploit chains.
When evaluated collectively, these incremental improvements can produce substantial operational value.
How refixs2.5.8a Differs from Major Releases
Understanding version hierarchy prevents unrealistic expectations.
| Major Release | Patch-Level Release (e.g., refixs2.5.8a) |
| Introduces new architecture | Refines existing structure |
| May break backward compatibility | Preserves compatibility |
| Requires retraining or migration planning | Minimal workflow disruption |
| Longer deployment cycle | Faster adoption window |
The strategic advantage of refixs2.5.8a lies in its non-disruptive enhancement model.
Real-World Implementation Example
Consider an enterprise application experiencing intermittent memory spikes during peak usage.
Instead of redesigning the application, engineers release refixs2.5.8a with:
- Improved garbage collection tuning
- Optimized concurrency handling
- Corrected exception management in edge scenarios
After deployment:
- Server resource consumption drops by measurable margins.
- Incident reports decline.
- User response times stabilize under load.
No new features are introduced, yet operational reliability significantly improves.
This illustrates the often underestimated value of precision patch releases.
Common Challenges in Deploying refixs2.5.8a
Even minor updates require disciplined governance.
Assumption of “Low Impact”
Teams sometimes treat patch updates as risk-free. In reality, even small code adjustments can introduce unintended interactions.
Insufficient Testing
Skipping staging validation increases exposure to integration conflicts.
Documentation Gaps
Clear documentation ensures alignment across development, operations, and compliance teams.
Version Fragmentation
Failure to standardize deployment may result in inconsistent environments across teams or regions.
Addressing these challenges ensures refixs2.5.8a delivers its intended benefits.
Strategic and Organizational Impact
Incremental version refinement plays a critical role in long-term digital resilience.
Risk Reduction
Frequent, controlled updates prevent technical debt accumulation.
Cultural Discipline
Organizations that adopt structured upgrade cycles foster stronger engineering governance.
Long-Term Scalability
Stable patch management ensures systems remain adaptable to future major releases.
Competitive Reliability
Consistency in performance and uptime directly influences user trust and brand credibility.
In mature digital ecosystems, operational excellence is built through disciplined incremental improvement not sudden transformation.
Long-Term Transformation Through Iterative Refinement
Sustainable system maturity is achieved through cumulative improvements.
A version like refixs2.5.8a contributes to:
- Stabilized performance baselines
- Reduced reactive engineering cycles
- Improved internal quality assurance frameworks
- Stronger deployment automation standards
Over time, these improvements compound.
Organizations that prioritize consistent patch-level upgrades often experience fewer catastrophic failures and smoother transitions during major architectural shifts.
Authority and Trust: Why Structured Versioning Matters Today
In modern digital infrastructure, trust is not built solely through innovation. It is built through reliability, predictability, and disciplined change management.
Version updates such as refixs2.5.8a reflect mature engineering governance. They demonstrate:
- Commitment to ongoing maintenance
- Responsiveness to operational feedback
- Security accountability
- Performance transparency
From an ethical perspective, maintaining secure and stable systems protects end users and stakeholders.
From a financial perspective, incremental optimization reduces downtime costs, regulatory exposure, and reputational risk.
From a strategic perspective, structured refinement builds long-term ROI by preserving architectural integrity.
In a landscape where digital failure can result in immediate global impact, disciplined version evolution is not optional it is foundational.
Frequently Asked Questions
1. What is refixs2.5.8a?
refixs2.5.8a is a structured version release that typically represents a patch-level update. It focuses on refining performance, improving stability, and correcting specific issues without introducing major architectural changes. It is designed to enhance reliability while maintaining backward compatibility.
2. Is refixs2.5.8a a major upgrade?
No, refixs2.5.8a is generally considered a minor or patch-level release. It improves existing functionality rather than introducing new core features. Such updates are intended to strengthen system performance and security without requiring disruptive migrations.
3. Why is refixs2.5.8a important for system stability?
refixs2.5.8a typically addresses identified bugs, performance inefficiencies, and potential vulnerabilities. By resolving these issues, it reduces system errors, enhances reliability, and ensures smoother operational performance in production environments.
4. Does refixs2.5.8a affect compatibility?
Patch-level releases like refixs2.5.8a are usually designed to preserve compatibility with existing integrations. They focus on refinement rather than structural change, minimizing disruption across dependent systems.
5. Should organizations prioritize installing refixs2.5.8a?
Yes, when validated in a staging environment, deploying refixs2.5.8a can strengthen performance, reduce operational risk, and improve security posture. Delaying structured patch updates may increase exposure to avoidable system instability.
6. How does refixs2.5.8a support long-term scalability?
refixs2.5.8a contributes to scalability by stabilizing performance baselines and preventing technical debt accumulation. Incremental refinements ensure systems remain adaptable and resilient, preparing infrastructure for future major upgrades.
Conclusion
refixs2.5.8a represents more than a simple version increment. It reflects disciplined engineering, operational refinement, and strategic stability.
While major releases attract attention, it is structured patch-level improvements that sustain long-term system integrity. Through performance optimization, security hardening, and compatibility assurance, refixs2.5.8a contributes to measurable operational resilience.
For organizations committed to reliability and scalable growth, disciplined adoption of such releases is not merely technical housekeeping it is a strategic imperative.